Poor password management a top data security threat in 2018
Experts say poor password management is a top data security threat in 2018. Bad passwords like “12345” and “password” remain go-to picks for many - and hackers everywhere thank you. Especially when you reuse them for multiple logins! Think your weak password isn't putting you at risk of a damaging data breach? Well...
Weak passwords a major security threat
In August, news broke that Western Australian government officials were using generic logins like “abcd1234” and “password123” (the latter used by nearly 1,500 employees), leaving systems across a number of government agencies vulnerable to hacking. Full access to every government system could be accessed via the password “Sumer123”.
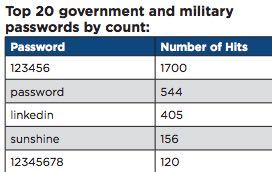
Anyone who’s read Seattle-based security specialist WatchGuard’s just published Q2 2018 Internet Security report won’t be surprised. In their investigation of passwords used for 355,000+ government and military accounts, WatchGaurd found that nearly half of all passwords associated with .GOV and .MIL email addresses are weak, 50 percent cracked within two days. “In fact, it only took us a few hours to find most of the cracked passwords,” say the report’s writers. Most commonly used passwords include “123456,” “password,” “linkedin,” “sunshine,” and “12345678”.
And those are just the passwords used by government and military employees. Civilians passwords were found weak 52 percent of the time. These passwords match up with those discovered in hacked LinkedIn data from 2012.
Reused passwords increase data security risks
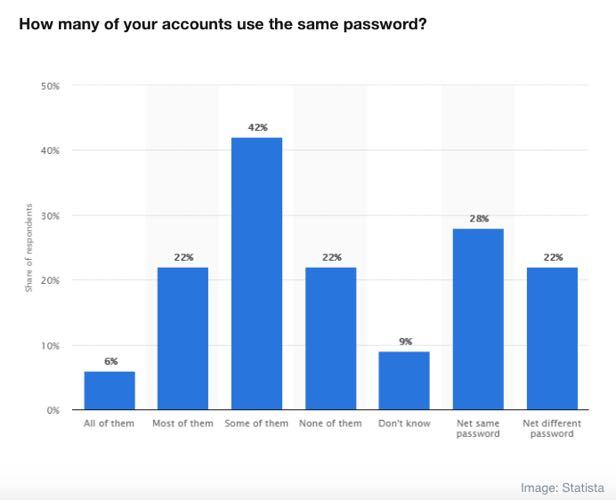
Users are making poor passwords choices, then doubling down by using the same passwords over and over again. Statista reports that even though 80 percent of those surveyed say cyber security is important, most people basically use the same passwords for multiple logins. And you might be surprised by who is doing this. Over the summer, a survey of 306 infosec professionals showed that 45 percent are committing the very crime they’ve been admonishing everyone else for: recycling passwords. Then again nearly half of all Italian phsyicians still smoke so go figure.
Credential stuffing a gift that keeps on giving
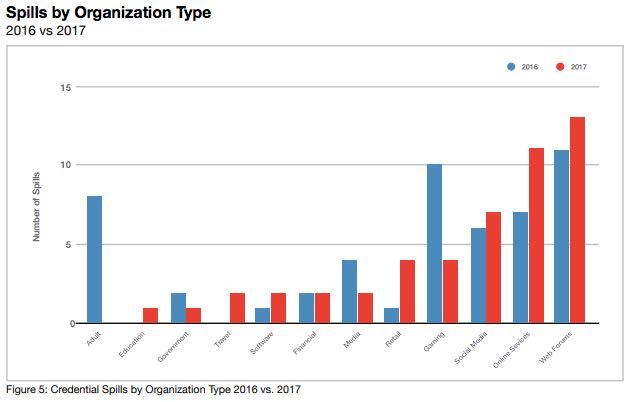
Reusing passwords is a bad idea. When login information gets leaked through a data breach (for example, that 2012 LinkedIn breach mentioned before), attackers can harvest passwords and user names, testing them across a range of websites and apps. If users are reusing the same login information, there’s no end to the number of sites and apps criminals can gain access to. This practice, known as credential stuffing, allows criminals to cause serious damage. Shape Security’s second annual Credential Spill Report indicates that credential spills result in global losses of $50 million a day, go undetected for 15 months on average, and leave no sector immune.
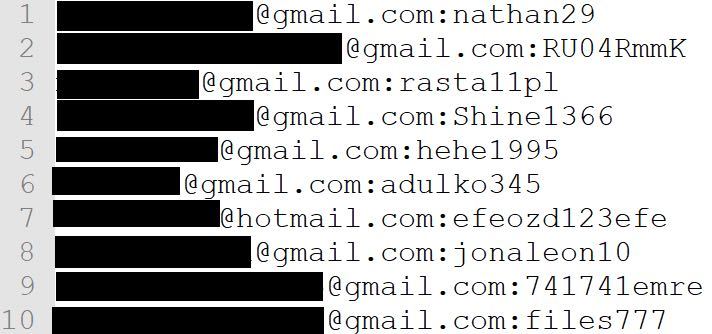
42 million passwords in clear text for the taking
Just this month, a massive database of close to 42 million email addresses and passwords in clear text was uploaded to a free, public, anonymous hosting service. Once the service discovered the breach, they shared the data with a security expert who determined the data matched up with that found in typical credential stuffing attacks: long lists of username/password pairs.
But this is just the latest in a string of credential stuffing incidents. British cosmetics retailer Superdrug reported in August that hackers accessed the email addresses and passwords of nearly 20,000 online shoppers. It was also widely reported in August that Air Canada had to reset the passwords for close to 20,000 profiles after it discovered hackers had managed to access email address and login information.
Data security best practices
It's never too late to take action. And, really, even taking just a few basic steps to improve your data security management practices can lead to increased safety for your personal or professional accounts. Here's what you can do to better protect your EuroDNS account.
Two-step verification for even stronger account protection
Two-step verification (available at EuroDNS) provides an additional layer of protection, stopping unauthorised access to your account. You'll be prompted to confirm your identity each time you want access, using a security code you'll receive in a text message in addition to your account password. The last thing you want is to lose control of your account. If that happens, you lose control of your domain names. With access to your domain control panel, a hacker will have no trouble changing your name and contact details to their own, taking ownership of your domains.
Domain privacy hides your contact details
You have the option to purchase domain privacy which protects the contact details - including your email address - that we are obligated to submit to WHOIS with every domain registration. Domain privacy ensures that the WHOIS database will replace your email address with proxy contact information for your domain, removing from public view your details.
Avoid sites which don’t use an SSL certificate
Fortunately, Google's efforts to create a 100 percent encrypted Internet make this one a pretty easy action to take. HTTPS-encrypted SSL certificates have become the standard for website security. SSL encrypts data between browsers and websites, making bank account information, personal details, login passwords, and anything else you want kept private less likely to fall into the hands of criminals.
Rethink your password management strategy
We know, we know. You've heard it all before. But, hopefully, these recent reports have convinced you that now is the time to improve your password strategy. Keep in mind a few general rules of thumb agreed on by the majority of security experts:
- The strongest passwords are 16 characters or more and include lower and upper-case letters as well as special characters and numbers.
- Nothing in the password should include anything related to you, such as pet names or your birthday, and it's a good idea to try to use phrases instead of words.
- Use different passwords for different accounts.
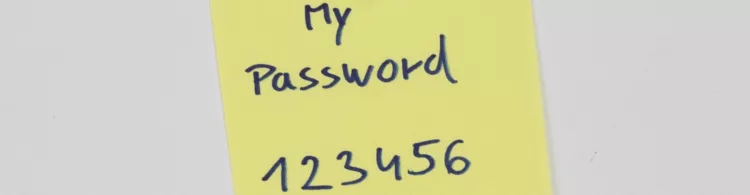
And, whatever you do, don't write your password down on a Post-it Note and stick it on your computer. Why make it easier than it already is to put your data security at risk?
Does your domain name affect your search engine ranking?
Related articles: