Is DNS-over-HTTPS (DoH) the best choice for DNS privacy?

The Internet Engineering Task Force’s (IETF) decision to adopt DNS-over-HTTPS (DoH) as a standard protocol for sending and receiving DNS queries and responses has many speculating that DoH could be the future of DNS privacy. But many are questioning whether acceptance and adoption of of DoH is the right move. Here's why.
DNSSEC not a silver bullet
The domain name system (DNS) protocol maps a domain name to the IP address of the server hosting that domain. This allows you to view a web page. But DNS queries have traditionally been sent without encryption. This makes them vulnerable to interception and manipulation. As such, for several years, the Internet industry has worked to secure DNS privacy by eliminating these kinds of DNS-related vulnerabilities.
The introduction of DNSSEC in 2006 was an important step towards ramping up the security of DNS protocol.
DNSSEC (Domain Name System Security Extensions) uses cryptographic keys to validate connections between a client end user and a domain name. It provides a security chain of trust that provides protection from DNS vulnerabilities via private and public encryption keys. These are used to validate every aspect of the DNS resolution process. Basically, this ensures that users are connecting with the right site, not a counterfeit.
That said, DNSSEC isn’t perfect. It can’t intercept incoming traffic so it doesn’t directly protect against denial-of-service (DoS) attacks. It doesn’t provide confidentiality of data, so it’s possible for a third party to look into a users’ DNS history. And if not properly secured, it can fall victim to cache poisoning and malicious redirection attacks.
Enter DNS-over-HTTPs.
DNS privacy improvements with DNS-over-HTTPS
The Internet industry has created various ways to overcome DNSSEC’s shortcomings, one of which is the IETF’s DNS-over-HTTPS (DoH) protocol.
DoH’s chief benefit is that it encrypts DNS requests through HTTPS protocol exchanges. This produces several positive outcomes:
- Protects against DNS hijacking and spoofing
- Man-in-the-middle defence
- Guaranteed DNS confidentiality
- Harder to share information with third-parties (governments, corporations)
All of these advantages are possible due to the fact that domain name resolution doesn’t require asking the public DNS infrastructure to resolve a domain. Instead, DoH relies on a direct connection between an end-user and a web server’s interface.
As a result, clients have greater control over their DNS queries. DoH guarantees that a client is provided accurate IP address information, eliminating opportunities for third parties to see what websites a user is trying to access.
Although its capabilities are greater than DNSSEC, DoH doesn’t entirely eliminate privacy-related vulnerabilities. The DoH protocol is designed to standardise HTTPS encodings for DNS queries. But it would still be possible for a third party to observe an initial connection request made prior to HTTPS encryption.
To insure maximum DNS privacy, DoH would work best in tandem with DNSSEC and other security measures which validate SSL Certificate Authorities (CAs) used for site connections.
DoH testing results
Google, Cloudflare, Facebook, and many others have already implemented DoH solutions. (The DNS Privacy Project offers a complete list of DoH test servers.) These solutions are designed to shave off resolution time, thus eliminating any window of opportunity for third parties to interfere.
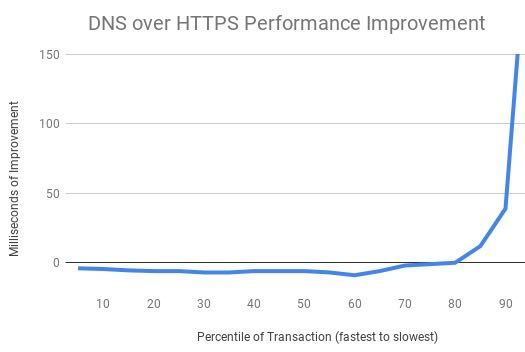
Earlier this year, Mozilla ran a test to gauge how well DoH performed, only to discover that in some case, query performance actually improved.
And Alphabet’s Intra app funnels – by default - now encrypts DNS queries to Google’s DoH-configured servers. Users also have the option to use Cloudflare’s DoH system or a custom DoH-capable server.
DNS-over-HTTPS criticisms
Despite increasing acceptance and adoption of DoH as a standard DNS protocol, not everyone is pleased. Security and privacy experts have raised objections related to operational risks, GDPR compatibility, and even the possibility that DoH could force users to cede privacy control to big Internet players like Cloudflare and Mozilla.
Regardless of Mozilla’s aforementioned research, some think a partnership which currently exists between Mozilla and Cloudflare has the potential to undermine privacy. Essentially, Mozilla will resolve domain names via Cloudflare’s DNS servers. This will not only allow Cloudflare to read everyone’s DNS requests, a security issue in and of itself, but also contribute to making the Internet even more centralised than it already is.
Others object to the fact that network administrators will have no way of looking at traffic and removing anything deemed objectionable.
It may be too soon to say whether or not DoH or other options like DNSCrypt or DNS Over TLS will become the new standard for DNS privacy. But one things is for sure: the question of how to best ensure DNS privacy won’t be going away any time soon. Watch this space for future developments.
And, as always, if you have questions about what you should be doing now to protect your own and your visitors' privacy, contact us at +352 263 725 250 or sales@eurodns.com. We'll be glad to offer assistance.
What are SSL stripping attacks and how can you prevent them?
Related articles: