5 ways to protect your small business from cyber attacks

Small business websites are an easy target for hackers as most are weak on cyber attack defence. To help keep your business safe from some of the most common cyber threats targeting small business websites, digital solutions expert DDI Development is here with solutions you can't afford to ignore.
Common cyber attack threats your small business faces
1. Malware
Malware is a piece of software used to destroy a company's files and collect sensitive data. It’s obtained once a user goes to a malicious website or downloads an infected attachment. Common malware types are viruses, trojans, and worms, created to infiltrate healthy files and spread on multiple devices.
The U.S. National Cyber Security Alliance has recently discovered that 60% of small businesses are forced to close within six months after a malware attack.
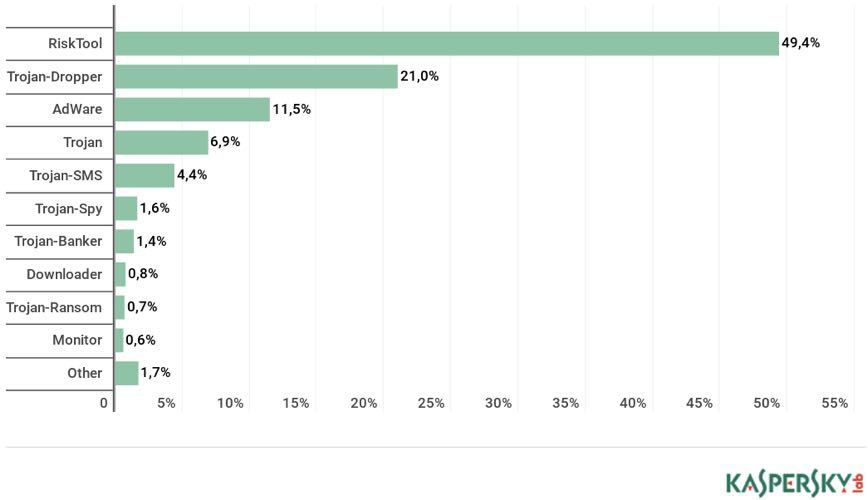
Most common malware in 2018, according to Kaspersky Lab
The reason is simple. According to that same report, the costs of cleaning up are unsustainable, starting from $690, 000 to over $1 million for middle-sized companies.
2. Password Attacks
Hackers use three common ways of obtaining passwords, targeting different weaknesses:
- Brute force: requires a specifically designed tool or script that automates password-guessing
- Dictionary method: the process of analysing password combinations to determine most commonly used for use in future attack
- Keylogger: perhaps the most dangerous, a special tracker receives access to a keylogger which is used to identify login credentials
A typical solution is two-factor verification which requires a user to approve their phone number or email address as well.
3. DDoS Attacks
Say you are releasing a new product. You've invested time and energy creating and marketing this product. You've raised your audience's expectations. Come launch day, users go to your website, prepared to make their purchase only to be greeted by a message that reads ‘Server Overloaded’.
Congratulations, you are a victim of a DDoS attack.
Distributed Denial of Service attacks render a target’s server unaccessible by overloading it. Hackers gather an army of zombie devices and start accessing the website from multiple computers, communicating with command and control servers.
This process is managed by multiple bots, also known as a botnet, each of which sends a large amount of network traffic to the target server.
4. Man-in-the-middle
Four years ago, cyber-criminals from Belgium targeted mid-sized European companies as well as big corporations. They stole €6 million by gaining access to email conversations and stealing confidential data.
This is a classic example of a man-in-the-middle attack. A hacker is literally sitting in the middle of a conversation, using your corporate accounts to access data. They can do this in a number of ways:
- Email hijacking: hackers gain access to corporate email accounts, spy on email contents, waiting for important data to come through
- Wi-Fi eavesdropping: attackers compromise your work router or infiltrate a public spot, and wait for members of your team to use it
- Session hijacking: whenever you access an infected page, hackers identify your device, steal cookies, and dig out sensitive information
These attacks can be prevented by using SMIME (Secure/Multipurpose Internal Main Extensions) that create an additional level of encryption for emails. To prevent Wi-Fi-based attacks, establish a certificate-based authentication. Only devices with the appropriate documentation can access the network.
5. SQL injection attacks
To store logins, passwords, personal data, and user activity records, businesses use database management systems. The most popular one is SQL.
An SQL injection is the simplest way of hitting a target. It works like this: a user submits an infected SQL statement (for instance, by filling out a registration form). A virus in the statement looks for security vulnerabilities in a database in order to exploit them.
A strong way to protect data from being leaked is to use multi-layered encryption of all database contents.
Small business security step-by-step
The best protection from cyber attack is preparation. Good news is that all of the following measures are easy to implement. Moreover, you don’t even need to hire a cybersecurity specialist, although consulting a custom software development company is certainly a good idea.
Step 1 - Back up your business data
All crucial business information and important files must be copied and stored in alternative safe storage, independent from your devices.
- Cloud backup services. Software will automatically create backup copies, preserving contents, formatting, and folder structure.
- USB drivers. Perfect for small files - use flash sticks to store receipts and important documentation but be sure to add password protection.
- Backup hard drives. Buy a clean hard drive and record copies of sensitive information there.
Step 2 - Monitor and protect your computer equipment and systems
Keeping your business secure requires keeping data management in constant check with the following methods:
- A firewall - software that blocks unauthorised access to devices and networks.
- A business version of an antivirus. Personal software will not be enough to cover multiple devices and servers.
- Use corporate VPN services to protect your location and IP.
- Ensure that DNS zone records are DNSSEC signed and your DNS resolvers are performing DNSSEC validation
Step 3 - Protect sensitive data
Rank your files based on their sensitivity, and be extra-careful about protecting the most potentially dangerous ones.
- Define what is stored and where. Constantly review your data storages to know where the most sensitive data is stored.
- Delete unnecessary files. The least data you have, the less damage can be inflicted to your company’s safety. Delete outdated files or archive them.
- Use an additional level of encryption. Even if your storage provides basic built-in protection, download an additional file protection tool that will encrypt selected data. And, of course, it goes without saying that you must use an SSL certificate to encrypt sensitive customer information.
Step 4 - Choose strong passwords and manage them
Educate your employees about the importance of strong protective combinations ("qwerty" is definitely off the table). Log-in credentials should be changed every quarter. All passwords should be stored in a password manager with built-in encryption. The most common standard is AES-256, used by governmental institutions and international corporations.
Step 5 - Educate your employees
No matter how much effort you put into protecting your business, it will be futile if an employee accesses a suspicious link from a work device or compromises work accounts.
- Clean desk rule - employees should not store confidential data like passwords and log-ins on post-its or in any printed form.
- Bring-own-device principle - be sure to control security measures on employees home devices and mobile phones if they use them for work.
- Discuss the dangers of removable media - what kind of data should never be stored on a flash drive, and which files can be transferred only after encryption.
- Enable ad blockers on employees devices and specify file download requirements.
Safeguard your business against cyber attacks
Practices like securing work devices, encrypting confidential files, and educating your team members may seem time-consuming. However, in reality, it’ll take you less than a month to implement all of the methods, described above. Securing your small business from cyber attacks simply requires planning ahead.
Don’t wait. Start implementing security practices right away, before it’s too late.
Author bio

DDI Development company brings a unique combination of business experience and solid technical proficiency to provide high-quality web and mobile digital solutions in a friendly and creative way. We help businesses achieve their goals by offering professional services. Our expertise spans into several industries including e-commerce, CRMs, e-learning platforms, recruitment and financial systems, etc. Our experienced team has delivered 150+ completed projects.
10 great education domain name ideas for eLearning websites
Related articles: